Azure IAM
Identity and Access Management
Azure provides tools to manage identities and control access, and it helps organizations secure their resources effectively.
| Feature | Description |
|---|---|
| RBAC |
|
| Azure AD |
|
| Azure AD DS & Azure MFA |
|
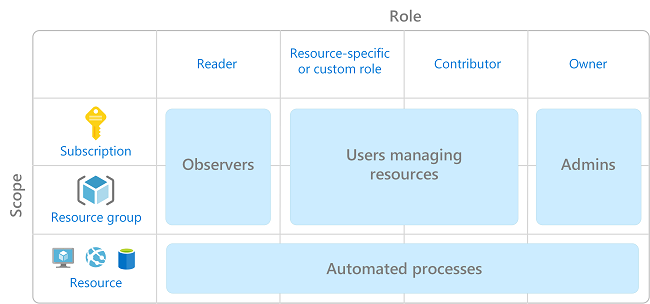
Role-Based Access Control (RBAC)
RBAC is built on Azure Resource Manager and provides detailed access control for Azure resources.
- Assigns users to roles with specific permissions and scope.
- Ensures users have only the access they need (least privilege).
- Helps separate duties across teams.
- Ideal for organizations with multiple resources and teams.
Example Scenario:
- Different teams manage specific resources (e.g., VMs, networks, databases).
- Each user gets only the access needed for their role, reducing risk.
Microsoft Entra ID
Previously known as "Azure Active Directory", Microsoft Entra ID is a cloud-based identity and access management service by Microsoft which allows you to control access to internal and external resources.
For more information, please see Microsoft Entra ID.
| Role | Description |
|---|---|
| IT Admins |
|
| App Developers |
|
| Subscribers |
|
Identity Protection
This feature automatically detects and assesses risks associated with user logins. Key functionalities include:
-
Automated Risk Detection
-
Detects suspicious logins (e.g., unusual locations or anonymous IPs)
-
Identifies password spray attacks (same password across multiple accounts)
-
Flags other risky sign-in behaviors
-
Automated Remediation
-
Triggers can be configured for risky logins
-
Can require MFA or blockng the login attempt
-
Manual Investigation
-
Allows administrators to review risky sign-ins
-
Can override automated actions
-
Supports custom investigation processes
-
Integration with SIEM
-
Export risk detection data to SIEM systems
-
Supports centralized monitoring and advanced analysis
Privileged Identity Management (PIM)
Microsoft’s Privileged Identity Management (PIM) protects administrator accounts and prevents unauthorized access, and it ensures that elevated privileges are granted only when needed.
| Feature | Description |
|---|---|
| Access Reviews | PIM requires regular reviews of administrator accounts, and Access Reviews are the process to ensure only necessary privileges remain assigned. |
| Just-In-Time Access | PIM enforces temporary elevation of privileges, and Just-In-Time Access is how eligible users request and gain those elevated roles only when needed. |
| Audit Trail | PIM logs all privileged activities, and the Audit Trail provides a detailed record of who activated roles, when, and what actions were taken, ensuring accountability. |
How "Just-In-Time Access" works
- Certain users are marked as eligible for administrator tasks
- These certain users do not have permanent permissions.
- When they need elevated access, they request role activation.
- They may complete multifactor authentication and provide a reason.
- If approval is required, an approver activates the role.
- The activation lasts for a limited time, and users must repeat the process for future tasks.